Welcome back to AssetIT’s ITSM Insight series. In our previous conversation, we looked at IT Asset Management’s (ITAM) critical role in Jira for cost control—a real key to efficiently reducing costs. Today, we set out to comprehend ITSM Compliance and Governance, another crucial aspect of IT service management.
Fundamentally, ITSM is about making sure that IT services are provided in a way that aligns with business requirements. Maintaining technology in line with business strategies is only one aspect of this alignment; another is making sure services are dependable, effective, and resilient. But how do we ensure that this alignment is not only maintained but optimized? This is where the ideas of governance and compliance are useful.
In ITSM, compliance refers to following the rules, laws, guidelines, and standards that govern the administration and provision of IT services. On the other hand, the framework for ITSM decision-making is provided by governance. It includes all of the rules, regulations, and procedures that specify how IT operations are managed and carried out. However, how do we put these ideas into practice in the actual ITSM world? This article will explore ITSM Compliance and Governance in more detail and show you which IT asset management solutions are best suited to completing this calculation.
Table of Contents
Understanding ITSM Compliance
Delving further into the domain of ITSM Compliance, we arrive at a nexus where the strategic coordination of IT services and strict adherence to standards meet. Ensuring that every IT service and process not only satisfies but surpasses the strict requirements outlined by legal, regulatory, and industry-specific standards is the goal of ITSM Compliance, which goes beyond simply checking off boxes on a regulatory checklist. This commitment to compliance covers a wide range of regulations, including industry-specific laws like HIPAA in the United States healthcare industry and international data protection laws like GDPR in the European Union. It also includes internal policies created to preserve organizational assets and uphold operational integrity.

It is impossible to overstate how important ITSM is to making this compliance possible. ITSM provides best practices and structured frameworks that act as a guide for creating, deploying, and overseeing IT services that are intrinsically compliant. This entails a thorough mapping of every service against the necessary legal and regulatory frameworks, guaranteeing that every IT process is founded on compliance from the start to the end. ITSM helps businesses proactively address possible compliance issues by integrating these factors into the lifecycle of IT services. This lowers the risk of non-compliance and the fines that come with it.
However, ITSM Compliance has an impact that goes beyond reducing risk. It is vital to the establishment of trust amongst the company’s numerous stakeholders, such as partners, clients, and government agencies. In a time when cybersecurity risks and data breaches are commonplace, an organization’s capacity to exhibit its dedication to compliance is critical. By assuring stakeholders of the company’s commitment to protecting sensitive data and upholding service dependability, it fosters a sense of security and confidence that is priceless in the current digital ecosystem.
The Role of ITSM Governance
Now, we move from the strictly regulated area of ITSM Compliance into the equally significant area of ITSM Governance. The foundation of ethical and successful IT service management is governance, which is similar to compliance in that it offers the strategic framework necessary to guarantee that decisions and actions are entirely consistent with the goals of the organization.
Overseeing decision-making and establishing accountability throughout the IT service lifecycle, governance serves as the framework for ITSM. It involves more than just following the rules. It also involves establishing a course of action that unites IT operations with the organization’s strategic objectives. A governance framework consists of a collection of procedures, rules, and guidelines. Therefore, it guarantees that every action is a step closer to realizing the organization’s vision.
Basically, governance instills in ITSM a culture of transparency and accountability. It guarantees that choices are made knowing exactly how they will affect the organization and its stakeholders. Building trust with clients, partners, and staff requires an open and accountable culture. Eventually, it demonstrates the company’s dedication to not just meeting but surpassing client expectations.
Governance symbolizes strong leadership, ethical management, and strategic focus in ITSM. It weaves ITSM components into a cohesive whole. This unity fosters organizational success. These concepts are vital for the future of IT excellence, beyond mere operations.
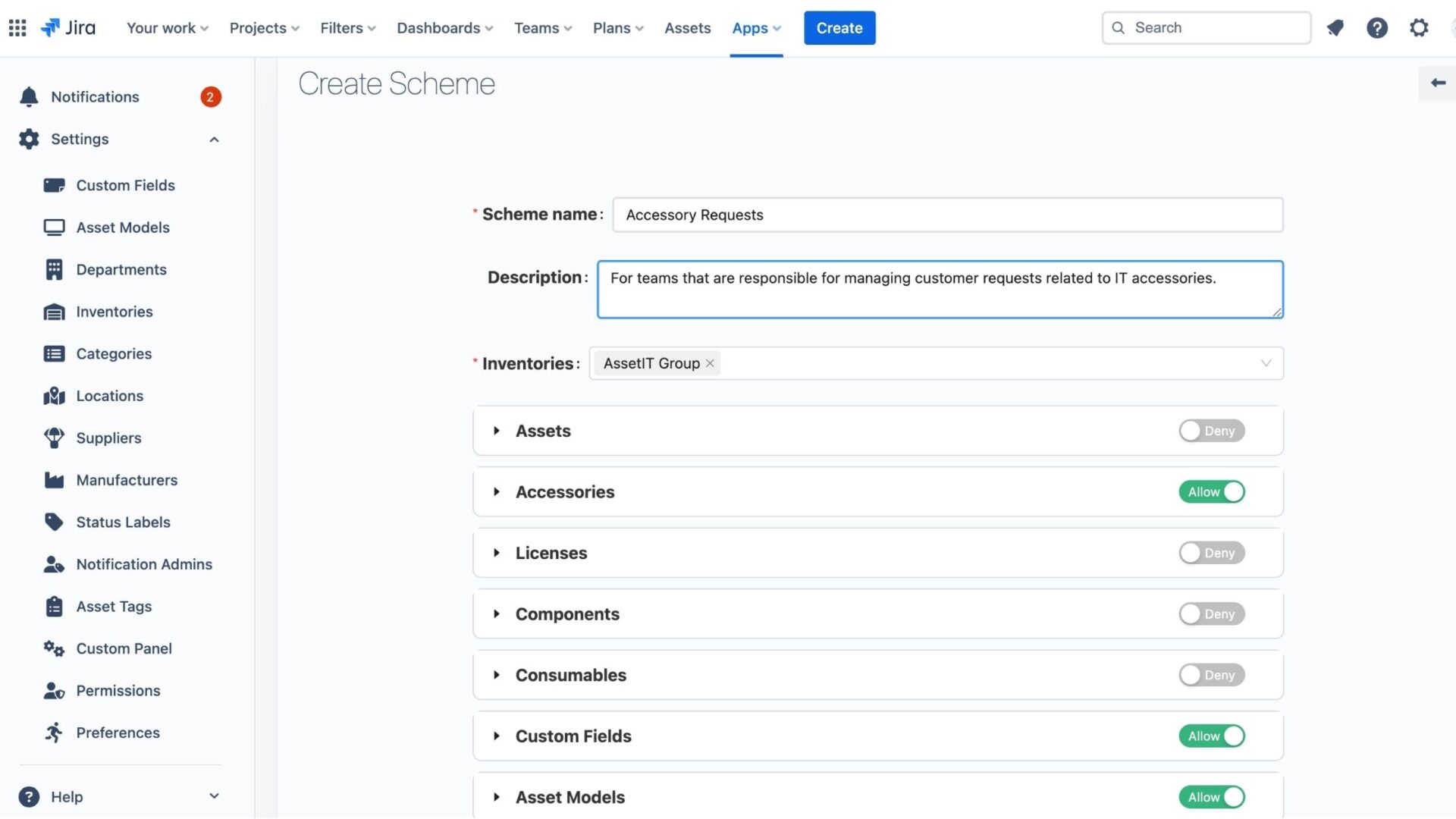
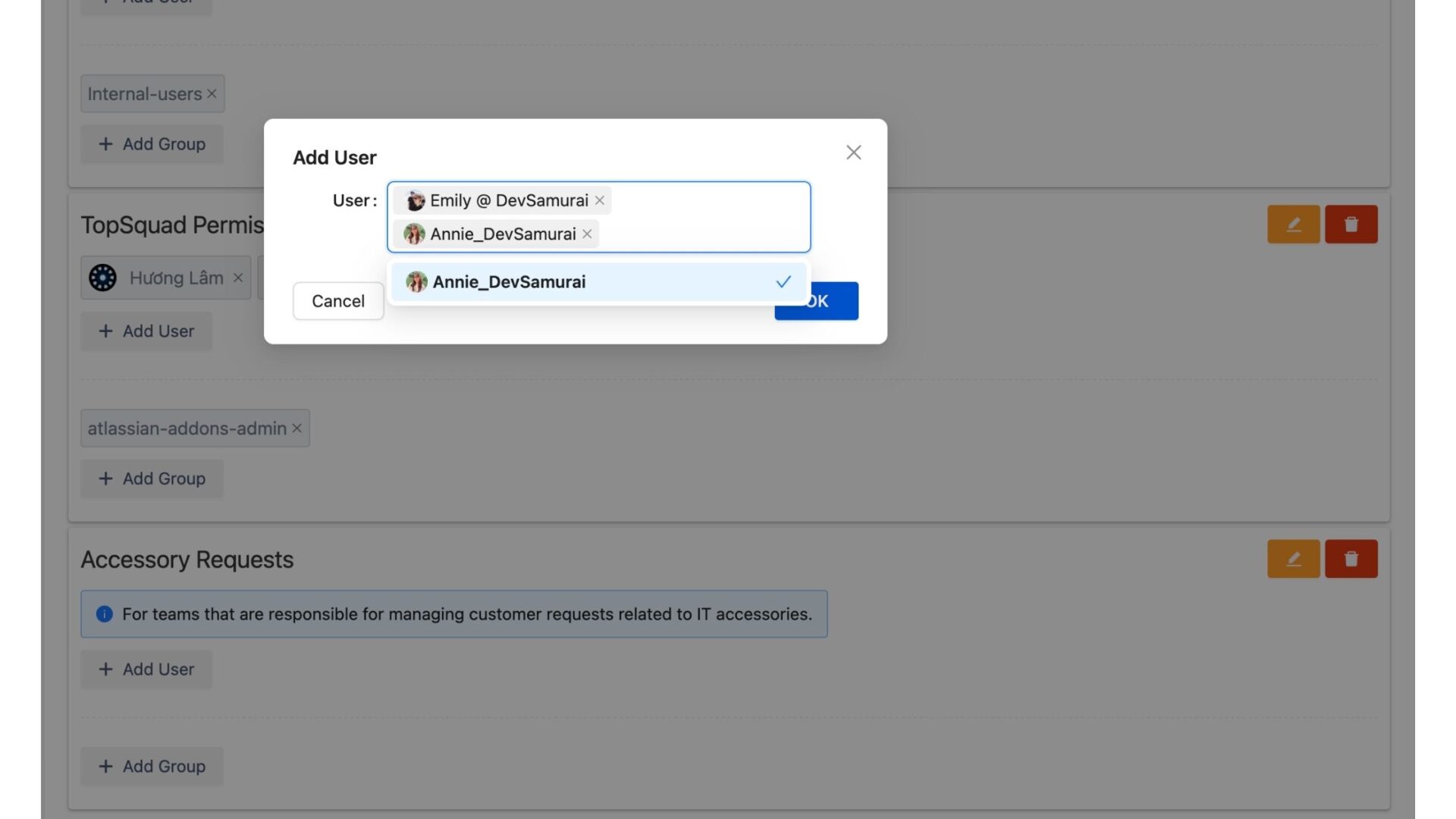
But how do we operationalize these concepts in the real world of ITSM? Here’s where ITSM tools like AssetIT shine. With features such as permission and permission schemes, AssetIT enables organizations to precisely control who has access to what information. This level of control is crucial for both ITSM compliance and governance. In other words, AssetIT can make sure that only authorized personnel are able to access sensitive information.
Permissions and Permission Schemes in ITSM Tools
It is essential to comprehend permissions and permission schemes in order to keep accessibility and security in ITSM in check. These controls make sure that only people with permission can access sensitive data and assets. Therefore, they are fundamental to ITSM compliance and governance practices. AssetIT provides an example of how ITSM tools can support governance and compliance goals with permission settings.
Deepening ITSM Compliance through Structured Permission Schemes
AssetIT’s permission schemes ensures strict adherence to compliance standards. Consider a scenario where an IT service company aims to streamline its operations and enhance efficiency. They categorized customer requests according to specific accountabilities. Faced with numerous requests for IT accessories, the company decided to implement a strategic permission scheme. Only the group in charge of IT accessories has access to pertinent resources thanks to this access control system. By doing this, the business guarantees compliance with standards and strengthens the security of its operations. In the end, it maximizes the use of available resources and improves the process of providing services as a whole.
Learn more about a success story in the IT industry: IT Service Company Case Study
Better Access Control for Risk Management
We have been talking about Risk Management in ITSM, and turns out that strictly following compliance and governance frameworks also contributes to empowering risk management efforts. With AssetIT, for example, permission settings safeguard IT operations and assets, minimizing potential threats and vulnerabilities. This means that individuals only have access to the information and assets necessary for their specific roles. Most significantly, it reduces the risk of unauthorized access or data breaches.
Conclusion
ITSM requires more than just regulatory compliance. Integrating compliance and governance is a strategic necessity that improves organizational resilience, agility, and trustworthiness. In this integration, the importance of ITSM solutions like AssetIT cannot be overlooked. These solutions provide the features and functionalities required to manage permissions, enforce policies, and monitor compliance in real-time. As the IT landscape changes, so too must our methods for ITSM governance and compliance.
If you have any inquiries or feature suggestions, please visit the Support Desk for prompt assistance.











Recent Comments